Ready to get started?
Secure Your Network Now
Don’t let threats take you by surprise. Reclaim control of your network’s security posture with Elisity. Unlock enhanced threat detection and policy management capabilities to achieve cybersecurity objectives confidently.
Not ready to schedule a demo?
See how Elisity solves for your top use cases in this self-guided tour.
Launch tour →
Schedule a Demo
Comprehensive Visibility
Discover, classify, and monitor every asset across your hybrid environment.
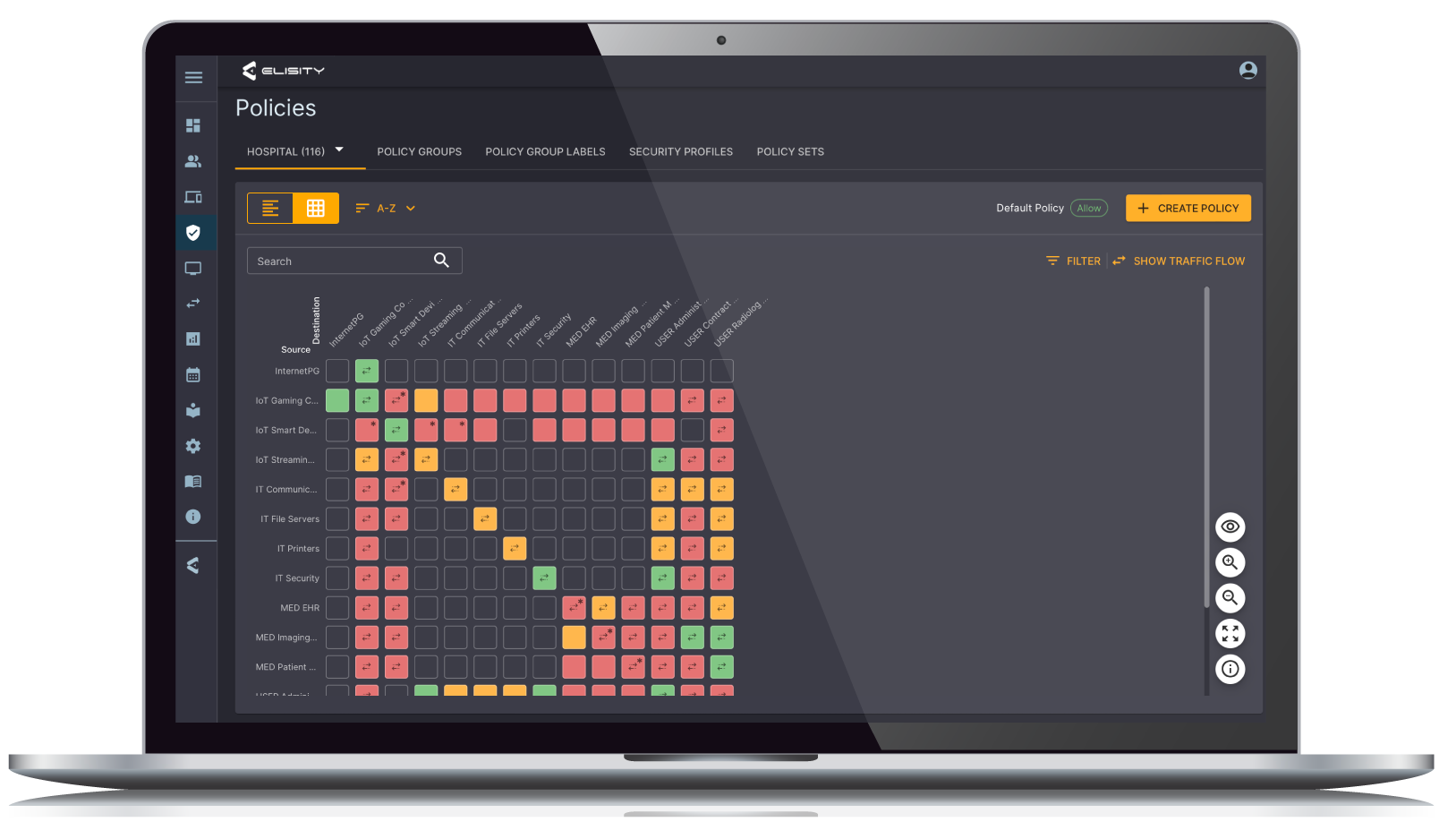
Granular Control
Enforce identity-based policies for users and devices with ease.
Lateral Movement Defense
Contain threats and limit blast radius with robust segmentation.
Simplified Management
Streamline policy administration across IT, OT, and IoT devices.
Continuous Compliance
Roll-out policies in phases for continuous refinement.
Zero Trust Enablement
Implement least privilege access based on identity and context.
“Elisity’s identity-based microsegmentation brings tremendous capabilities to our security stack as a critical control point for containing ransomware, blocking malicious lateral network traffic and minimizing incident blast radius, and Elisity features prominently for our present and forward-looking security posture, allowing us to easily adjust to new regulatory as well as threat landscape developments.”

Aaron Weismann
CISO at Main Line Health
“We deployed it at two of our sites in less than an hour, and by the next day, we were confidently implementing policies. This unprecedented speed and effectiveness soon made Elisity an indispensable part of our network security strategy across our manufacturing sites, protecting thousands of managed IT assets as well as our growing number of unmanaged IoT and OT assets.”

Max Everett
CISO at Shaw Industries